IDP Generic — что это такое и стоит ли этого опасаться?
Во время установки/запуска того или иного приложения ваш антивирус может начать ругаться об угрозе в лице IDP Generic. Сегодня мы поведаем вам, что это за «зверь» такой и стоит ли его вообще бояться.
Что такое IDP Generic?
Главное — не паникуйте! Дайте угадаем: на вашем компьютере установлена бесплатная версия Avast или AVG? Если ответ — да, то вам не о чем переживать, потому как найденный файл с IDP Generic, скорее всего, является ложной тревогой.
Задокументировано бесчисленное количество случаев, когда подобные антивирусы находили IDP Generic в совершенно легальных и безопасных файлах. Например, некоторые пользователи утверждают, что у них данный вирус был обнаружен в только что загруженной игре из Steam. Как вы понимаете, это попросту невозможно.
Почему возникают эти ложные тревоги? Четкий ответ на этот вопрос дать сложно, но есть предположения, что причина — это устаревшая база данных бесплатного антивируса. Также не стоит исключать и простой баг. Так или иначе если вы уверены, что с файлом, помеченным IDP Generic, все нормально — верните его из карантина и добавьте в исключения. И обязательно не забудьте обновить свой антивирус!
Но вот куда более важный вопрос: а может IDP Generic быть не ложной тревогой, а реальной угрозой? Ответ — конечно же может. Если он был, к примеру, обнаружен в совершенно незнакомом для вас файле, который лежит где-то в недрах ОС Windows, — это может быть вирус! Установите на свой ПК антивирус понадежней (либо и вовсе воспользуйтесь Защитником Windows) и запустите глубокое сканирование системы, а затем избавьтесь от угрозы!
Опасен ли вирус idp.heur.26?
аваст — хреновый антивирус. У многих подобные фацлы были безвредными и аваст их считал вирусами, хотя это были файлы стима или прочих безвредных программ. А что за драйвер апдейтер и откуда вы его качали?
Владимир ТитаренкоУченик (167) 1 год назад
программа для обновления драйверов, качал с официального сайта
a2cat a2cat Мастер (1424) Владимир Титаренко, тогда скорее всего ложное срабатывание. Уберите файл из карантина и продолжайте работать
Похожие вопросы
IDP.HEUR.26 Malware: A Complete Removal Guide
The inclusion of “IDP” in the detection name represents “Identity Protection,” indicating that the detection is rooted in analyzing the behavior of the file rather than relying solely on its signature or known attributes. The “HEUR” portion signifies “Heuristic,” implying that the detection is carried out using a collection of rules and algorithms specifically designed to identify potential threats that are previously unknown or unseen.
The specific number “26” serves as a unique identifier designated to this specific type of detection by Avast. It is crucial to acknowledge that not all detections with this name are inherently malicious, as certain legitimate software may display behavior that can trigger this particular type of detection.
Brendan Smith
IT Security Expert
It is better to prevent, than repair and repent!
When we talk about the intrusion of unfamiliar programs into your computer’s work, the proverb «Forewarned is forearmed» describes the situation as accurately as possible. Gridinsoft Anti-Malware is exactly the tool that is always useful to have in your armory: fast, efficient, up-to-date. It is appropriate to use it as an emergency help at the slightest suspicion of infection.

Gridinsoft Anti-Malware 6-day trial available.
EULA | Privacy Policy | Gridinsoft
Subscribe to our Telegram channel to be the first to know about news and our exclusive materials on information security.
Any type of malware exists with the only target – generate profits on you 1 . And the programmers of these things are not thinking of morality – they utilize all available methods. Taking your data, getting the payments for the promotions you watch for them, and exploiting your CPU and GPU to mine cryptocurrencies is not the full list of what they do. Do you like to be a riding horse? That is a rhetorical question.
This Article Contains:
What does the pop-up with IDP.HEUR.26 detection mean?
AVG consistently flags IDP.HEUR.26 virus for detection. It seems to re-enable itself despite having previously turned off AVG’s passive scanning and automatic downloads. My main antivirus software is Norton, and after conducting multiple scans with it, it hasn’t identified any issues. I’m inclined to believe it might be a false positive.
I’ve relocated the files to quarantine on numerous occasions, but they keep reappearing. Is there any possibility that this file could pose any genuine threat? from reddit
The IDP.HEUR.26 detection you can see in the lower right corner is displayed to you by Avast or AVG. That anti-malware program is good at scanning but prone to be unreliable. It is defenseless to malware invasions. It has a glitchy user interface and problematic malware removal features. Therefore, the pop-up states concerning the IDP.HEUR.26 is rather just a notification that Defender has found it. You will likely need to use another anti-malware program to remove it.
The exact IDP.HEUR.26 infection is a nasty thing. It digs into your computer disguised as a part of something legitimate or as a part of the tool you downloaded from a forum. After that, it makes everything weakens your system. At the end of this “party”, it downloads other malicious things – ones that are wanted by cybercriminals who control this virus. Hence, it is almost impossible to predict the effects of IDP.HEUR.26 actions. And unpredictability is one of the most unwanted things when we are talking about malware. That’s why it is better not to choose at all and don’t let the malware complete its task.
Threat Summary:
Is IDP.HEUR.26 dangerous?
As I have pointed out previously, non-harmful malware does not exist. And IDP.HEUR.26 is not an exclusion. This malware changes the system setup and alters the Group Policies and Windows registry. All of these elements are crucial for proper system functioning, even in cases when we are not talking about system safety. Therefore, the virus IDP.HEUR.26 contains, or which it will download after some time, will squeeze out maximum revenue from you. Cybercriminals can grab your personal information and sell it on the black market. Using adware and browser hijacker functions embedded in IDP.HEUR.26 virus, they can make money by showing you the ads. Each view gives them a penny, but 100 views per day = $1. 1000 victims who watch 100 banners per day – $1000. Easy math, but sad conclusions. It is a bad choice to be a donkey for crooks.
How did I get this virus?
It is hard to trace malware’s origins on your computer. Nowadays, things are mixed, and spreading ways chosen by adware five years ago can be utilized by spyware these days. But if we abstract from the exact spreading tactic and think of why it works, the answer will be pretty uncomplicated – low level of cybersecurity awareness. Individuals press on advertisements on weird websites, open the pop-ups they receive in their web browsers, and call “Microsoft tech support” believing that the odd banner that says about malware is true. It is very important to recognize what is legitimate – to prevent misunderstandings when figuring out a virus.
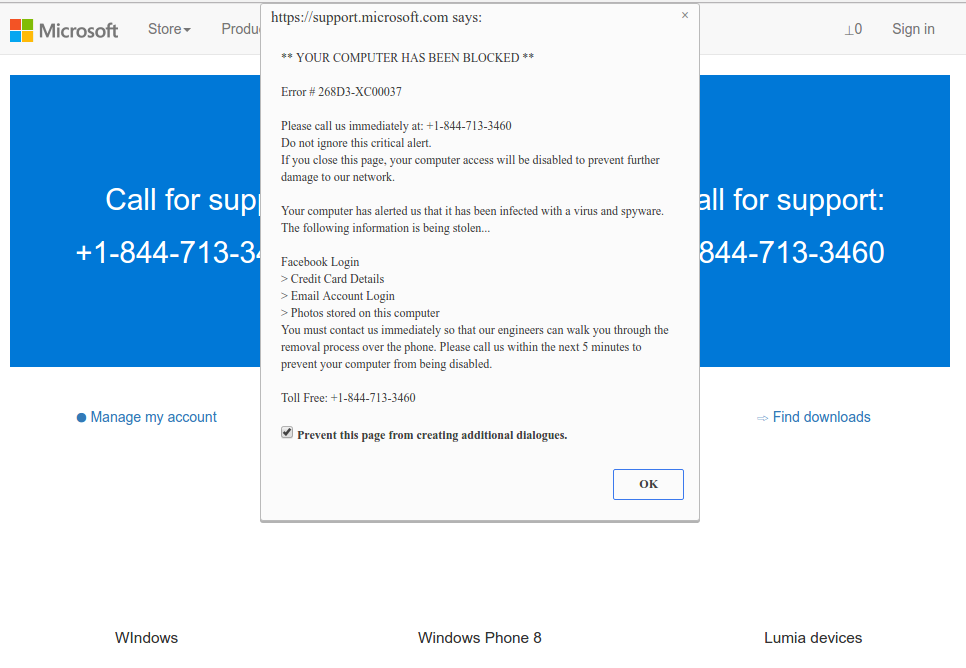
Microsoft Tech Support Scam
Nowadays, there are two of the most extensive ways of malware distribution – lure e-mails and injection into a hacked program. While the first one is not so easy to avoid – you should know a lot to recognize a counterfeit – the 2nd one is easy to solve: don’t utilize cracked applications. Torrent trackers and other sources of “free” applications (which are paid but with a disabled license checking) are a giveaway point of malware. And IDP.HEUR.26 is just among them.
How to remove the IDP.HEUR.26 from my PC?
IDP.HEUR.26 malware is very difficult to eliminate by hand. It places its data in multiple places throughout the disk and can get back itself from one of the elements. In addition, various alterations in the Windows registry, networking settings, and Group Policies are quite hard to identify and change to the initial. It is better to use a special program – exactly, an anti-malware app. GridinSoft Anti-Malware will fit the most ideal for virus elimination purposes.
Remove IDP.HEUR.26 with Gridinsoft Anti-Malware
We have also been using this software on our systems ever since, and it has always been successful in detecting viruses. It has blocked the most common Trojans as shown from our tests with the software, and we assure you that it can remove IDP.HEUR.26 as well as other malware hiding on your computer.

To use Gridinsoft for remove malicious threats, follow the steps below:
1. Begin by downloading Gridinsoft Anti-Malware, accessible via the blue button below or directly from the official website gridinsoft.com.
2. Once the Gridinsoft setup file (setup-gridinsoft-fix.exe) is downloaded, execute it by clicking on the file.

3. Follow the installation setup wizard’s instructions diligently.

4. Access the «Scan Tab» on the application’s start screen and launch a comprehensive «Full Scan» to examine your entire computer. This inclusive scan encompasses the memory, startup items, the registry, services, drivers, and all files, ensuring that it detects malware hidden in all possible locations.

Be patient, as the scan duration depends on the number of files and your computer’s hardware capabilities. Use this time to relax or attend to other tasks.
5. Upon completion, Anti-Malware will present a detailed report containing all the detected malicious items and threats on your PC.

6. Select all the identified items from the report and confidently click the «Clean Now» button. This action will safely remove the malicious files from your computer, transferring them to the secure quarantine zone of the anti-malware program to prevent any further harmful actions.

8. If prompted, restart your computer to finalize the full system scan procedure. This step is crucial to ensure thorough removal of any remaining threats. After the restart, Gridinsoft Anti-Malware will open and display a message confirming the completion of the scan.
Remember Gridinsoft offers a 6-day free trial. This means you can take advantage of the trial period at no cost to experience the full benefits of the software and prevent any future malware infections on your system. Embrace this opportunity to fortify your computer’s security without any financial commitment.
Trojan Killer for “IDP.HEUR.26” removal on locked PC
In situations where it becomes impossible to download antivirus applications directly onto the infected computer due to malware blocking access to websites, an alternative solution is to utilize the Trojan Killer application.

There is a really little number of security tools that are able to be set up on the USB drives, and antiviruses that can do so in most cases require to obtain quite an expensive license. For this instance, I can recommend you to use another solution of GridinSoft — Trojan Killer Portable. It has a 14-days cost-free trial mode that offers the entire features of the paid version. This term will definitely be 100% enough to wipe malware out.
Trojan Killer is a valuable tool in your cybersecurity arsenal, helping you to effectively remove malware from infected computers. Now, we will walk you through the process of using Trojan Killer from a USB flash drive to scan and remove malware on an infected PC. Remember, always obtain permission to scan and remove malware from a computer that you do not own.
Step 1: Download & Install Trojan Killer on a Clean Computer:
1. Go to the official GridinSoft website (gridinsoft.com) and download Trojan Killer to a computer that is not infected.

2. Insert a USB flash drive into this computer.
3. Install Trojan Killer to the «removable drive» following the on-screen instructions.

4. Once the installation is complete, launch Trojan Killer.
Step 2: Update Signature Databases:
5. After launching Trojan Killer, ensure that your computer is connected to the Internet.
6. Click «Update» icon to download the latest signature databases, which will ensure the tool can detect the most recent threats.

Step 3: Scan the Infected PC:
7. Safely eject the USB flash drive from the clean computer.
8. Boot the infected computer to the Safe Mode.
9. Insert the USB flash drive.
10. Run tk.exe
11. Once the program is open, click on «Full Scan» to begin the malware scanning process.

Step 4: Remove Found Threats:
12. After the scan is complete, Trojan Killer will display a list of detected threats.

13. Click on «Cure PC!» to remove the identified malware from the infected PC.
14. Follow any additional on-screen prompts to complete the removal process.

Step 5: Restart Your Computer:
15. Once the threats are removed, click on «Restart PC» to reboot your computer.
16. Remove the USB flash drive from the infected computer.
Congratulations on effectively removing IDP.HEUR.26 and the concealed threats from your computer! You can now have peace of mind, knowing that they won’t resurface again. Thanks to Gridinsoft’s capabilities and commitment to cybersecurity, your system is now protected.
Another detections from Avast
- Posts not found
How to Remove IDP.HEUR.26 Virus
Name: IDP.HEUR.26
Description: If you have seen a message showing the “IDP.HEUR.26 found”, it seems that your system is in trouble. The IDP.HEUR.26 virus was detected, but to remove it, you need to use a security tool. Windows Defender, which has shown you this message, has detected the malware. However, Defender is not reliable — it is prone to malfunction when it comes to malware removal. Getting the IDP.HEUR.26 malware on your PC is an unpleasant thing, and removing it as soon as possible must be your primary task.
Operating System: Windows
Application Category: Trojan
IDP.HEUR.26 (Malware Removal Guide)
IDP.HEUR.26 is the detection name for threats detected by antivirus programs. This type of threat is malicious and can do unwanted actions to the computer it infects.
Your antivirus software may have informed you of this threat because it discovered the specific malware on your computer during the program’s routine scans.
These detection warnings should not be taken lightly since it means that your device is vulnerable and can be exploited by malicious actors.
You should take appropriate actions once the anti-malware software notices these types of threats on your device. It is always best to get rid of it before it can do much harm to the computer.
These threats are often acquired through spam emails, infected websites, or by clicking on a link in an email. Once installed on the computer system, IDP.HEUR.26 will begin to spread across your PC via Windows System files.
Hackers may be able to view all the data on your computer and even take over its operation once they have been deployed on the system.
Threats like these should not be allowed to remain on the computer for an extended period because they may result in irreparable harm.
Users who have IDP.HEUR.26 on their devices are most likely to face the following problems.
- Sudden issues with internet connection and applications
- Freezing or slowdowns in computer performance
- Difficulties opening documents or accessing files.
- Pop-ups appear online or when browsing.
- Overheat and high CPU usage.
These kinds of discoveries are particularly risky since they can be used to attack unsuspecting users online by stealing their financial information, privacy passwords, and other data.
It’s critical to get rid of this particular virus as soon as you suspect you may have been impacted by it. Typically the antivirus that has detected this threat should be enough to get rid of the said malware.
Unless certain circumstances prevent the anti-malware program from eliminating the said malware, you may utilize Malwarebytes Anti Malware to help you remove the virus instead. You may follow the steps below to eliminate the threat that has been discovered in your system using Malwarebytes.
Our team has recently tested this procedure and has confirmed that it is still working and up-to-date. Learn More
Remove IDP.HEUR.26 with Malwarebytes Anti-Malware
We have also been using this software on our systems ever since, and it has always been successful in detecting viruses. It has blocked many known computer threats as shown from our tests with the software, and we assure you that it can remove IDP.HEUR.26 as well as other malware hiding on your computer.

Not to mention, it is free to use and does not come at any cost to remove the viruses it finds on your computer.
To use Malwarebytes and remove malicious threats from the computer, follow the steps below:
1. Download Malwarebytes by clicking the button below, as we have made an additional and in-depth tutorial on how to use it. Otherwise, you may go to their official website via Malwarebytes.com (Avoid misspelling as it may lead to scams).
2. Visit their download section and start a Free Download to begin installing the software on your computer.  3. Once the Malwarebytes setup file (MBsetup.exe) has finished downloading, open the executable file in File Explorer, then right-click the setup and select run as administrator to give the highest system authority and make sure Malwarebytes is installed correctly.
3. Once the Malwarebytes setup file (MBsetup.exe) has finished downloading, open the executable file in File Explorer, then right-click the setup and select run as administrator to give the highest system authority and make sure Malwarebytes is installed correctly.  4. Make sure to carefully follow the installation setup wizard’s instructions and provide the relevant information it requires. You will be prompted with questions such as Personal or Business Use, Email Address, and others.
4. Make sure to carefully follow the installation setup wizard’s instructions and provide the relevant information it requires. You will be prompted with questions such as Personal or Business Use, Email Address, and others.  5. From the application’s home screen, go to the scan tab and begin running a system scan. This will scan the whole computer, including memory, startup items, the registry, and the file system. This is done so not only the residuals of IDP.HEUR.26 but also other trojan viruses hiding in the system can be detected.
5. From the application’s home screen, go to the scan tab and begin running a system scan. This will scan the whole computer, including memory, startup items, the registry, and the file system. This is done so not only the residuals of IDP.HEUR.26 but also other trojan viruses hiding in the system can be detected.  6. Since it can take a while, you should either relax and wait for it to finish or find something else to do. The length of the scan depends on the size of the files you have and the hardware capabilities of your computer. Here are some ways to make scanning faster.
6. Since it can take a while, you should either relax and wait for it to finish or find something else to do. The length of the scan depends on the size of the files you have and the hardware capabilities of your computer. Here are some ways to make scanning faster.
7. Once the scan is finished, Malwarebytes will show the malicious viruses and threats it found on your PC. IDP.HEUR.26 will also show up on the detection results, and it will show up in a threat name such as PUP.Optional.OpenCandy, and many more.  8. Select all the detected files from the report and click the quarantine button to remove the malicious items from the computer into the protected safe quarantine zone of the anti-malware program so that they would not affect and do malicious actions the PC again.
8. Select all the detected files from the report and click the quarantine button to remove the malicious items from the computer into the protected safe quarantine zone of the anti-malware program so that they would not affect and do malicious actions the PC again.  9. After placing the virus files in the program’s quarantine, it may prompt you to restart the computer to finalize the full system scan procedure. Please restart your computer if prompted, as it is essential. After the restart, Malwarebytes will open and display a message that the scan was complete.
9. After placing the virus files in the program’s quarantine, it may prompt you to restart the computer to finalize the full system scan procedure. Please restart your computer if prompted, as it is essential. After the restart, Malwarebytes will open and display a message that the scan was complete.
Note: Don’t forget to delete the quarantined files afterward.
Simply quarantining the malware files is not enough to make sure they are completely removed. This is a very common misconception: once you click the quarantine button, it is all good and gone.
But, while its effects and harmful activities are halted, the malware is still in the system, only placed in the anti-malware program’s quarantine folders. To completely remove it from the computer, go to Detection History from the home screen, select all Quarantined items, and click Delete.

You have successfully removed IDP.HEUR.26 as well as the hidden threats on your computer. Rest assured they would not resurface again since Malwarebytes offers a premium trial for 14 days, so you could take advantage of it for free and prevent malware from infecting your system.
While the detection and removal of malware are free for Malwarebytes, the premium versions include real-time protection that ensures your computer is safe all the time. Although we encourage you to use the premium trial, you are free to purchase the full version if you find it useful.
For a better and safer web browsing experience, we’ve provided a few security measures and advice below that will safeguard your browser and computer from harmful threats like worms, malware, trojans, keyloggers, stealers, and other kinds of computer viruses that will harm user data.
Protective measures for better overall security
Removing the malicious detections from the computer is one thing; keeping it secure for the future and a long period is a different thing and will require certain things to make sure you are secured, especially if you do not know most of the ins and outs of the device you are using.
Cybercriminals are always stepping up their game to make sure they infect users and extract data and money from them.
We encourage you to take the actions listed below to ensure complete security before leaving this page because we strongly promote web security and having a secure online presence.
Safeguard your data and privacy online by using a VPN application
VPNs, also known as virtual private networks, guarantee your safety and complete anonymity while you browse the internet.
In contrast to a firewall, which monitors and blocks potentially harmful connections in the network, A VPN hides the user’s connection via a tunnel so that it would appear to third parties as a different IP address and location.
This ensures that your data won’t be leaked because the program hides it. Be aware that visiting infected websites may cause your IP address and location to be disclosed; however, if you use a VPN, this will prevent your true IP address from being revealed to malware actors.
Use a firewall to prevent cyber attacks
A security firewall is required for every internet connection that is made. It is an essential tool that enhances security and stops online attacks.
Through a security mechanism, it controls incoming and outgoing network connections on your system and network and filters the undesirable ones. Consider it a further barrier against malicious assaults and zero-day exploits.
Bottom Line
Always make sure that your device is protected against sneaky exploits and stealthy cyberattacks. While taking precautions and avoiding dubious websites are crucial, having a solid line of defense is essential to ensuring the security of your network and data.
If you experience another malware issue, please visit our website to find a solution for your problem or get in touch with us, and SecuredStatus will be happy to assist you once again.
Millan Nava
Millan Nava, an adept Information Security Analyst, brings a decade of hands-on expertise in cybersecurity. His area of expertise is in conducting a thorough analysis of malicious software, revealing its susceptibilities, and providing pragmatic, user-friendly methods for removal. He created this website to serve as a navigational aid for the security of all internet users.
Let us know what you think
Our dedication to site improvement is a continuous journey. Your feedback is vital in enhancing the user experience and keeping our platform valuable.