Tx\Rx bandwidth limit на 2950-той Сиське «( . )( . )» ?
Прошу прощения) за нескромный вопрос)) но мне раньше не доводилось иметь длительные отношения с коммутаторами от Cisco =)) Как настроить ограничение пропускной способности (bandwidth limit) на конкретный порт ? К примеру порт Fa0/24 (Rx 128 kbps)(Tx 512 kbps)

Architector120
18.01.16 16:41:16 MSK

conf t int fa0/24 traffic-shape # хз не помню rate-limit # аналогично end redixin ★★★★
( 18.01.16 16:43:38 MSK )
Ответ на: комментарий от redixin 18.01.16 16:43:38 MSK

Хотя такое может не прокатить на 2950
redixin ★★★★
( 18.01.16 16:46:10 MSK )

хмм.. вот список всех доступных команд на порт Fa0/24
cisco(config)#interface fastEthernet 0/24 cisco(config-if)#? Interface configuration commands: arp Set arp type (arpa, probe, snap) or timeout auto Configure Automation bandwidth Set bandwidth informational parameter carrier-delay Specify delay for interface transitions cdp CDP interface subcommands channel-group Etherchannel/port bundling configuration channel-protocol Select the channel protocol (LACP, PAgP) default Set a command to its defaults delay Specify interface throughput delay description Interface specific description dot1x Interface Config Commands for 802.1x duplex Configure duplex operation. exit Exit from interface configuration mode fair-queue Enable Fair Queuing on an Interface help Description of the interactive help system hold-queue Set hold queue depth ip Interface Internet Protocol config commands keepalive Enable keepalive lacp LACP interface subcommands load-interval Specify interval for load calculation for an interface logging Configure logging for interface mac MAC interface commands mac-address Manually set interface MAC address mls mls interface commands mvr MVR per port configuration no Negate a command or set its defaults pagp PAgP interface subcommands random-detect Enable Weighted Random Early Detection (WRED) on an Interface rmon Configure Remote Monitoring on an interface service-policy Configure QoS Service Policy shutdown Shutdown the selected interface snmp Modify SNMP interface parameters spanning-tree Spanning Tree Subsystem speed Configure speed operation. storm-control storm configuration switchport Set switching mode characteristics timeout Define timeout values for this interface transmit-interface Assign a transmit interface to a receive-only interface tx-ring-limit Configure PA level transmit ring limit udld Configure UDLD enabled or disabled and ignore global UDLD setting Architector120
( 18.01.16 17:11:43 MSK ) автор топика
Ответ на: комментарий от Architector120 18.01.16 17:11:43 MSK

Ну да, это походу из тех свичей что так совсем не умеют. Могу ошибаться
redixin ★★★★
( 18.01.16 17:15:05 MSK )
Ответ на: комментарий от redixin 18.01.16 17:15:05 MSK

На некоторых ресурсах пишут что нужно править системный конфиг, но подробного описания процедуры нет
Architector120
( 18.01.16 17:20:25 MSK ) автор топика
Ответ на: комментарий от Architector120 18.01.16 17:11:43 MSK
bandwidth Set bandwidth informational parameter Этот параметр отвечает за пропускную способность интерфейса читай мануал по этому параметру.
Impact of Transmit Ring Size (tx-ring-limit)
Technology Resources » QoS Mechanisms » Impact of Transmit Ring Size (tx-ring-limit) Output interface queues in most software switching platforms contain a software-only component and a FIFO queue shared between the CPU and the outgoing interface. That FIFO queue is usually organized as a ring structure, and its maximum size can be controlled with the tx-ring-limit parameter in Cisco IOS. The impact of that parameter should be obvious: larger tx-ring-limit values cause more delay and jitter, resulting in reduced quality-of-service of time-critical applications (like voice-over-IP) over low-speed interfaces. A series of tests performed in a small tightly controlled test-bed quantifies the actual impact.
Overview
The default value of tx-ring-limit is a good compromise between the latency/jitter requirements of medium speed links and increased CPU utilization due to I/O interrupts caused by low tx-ring-limit values. On low-speed links (128 kbps and below), the tx-ring-limit should be decreased to 1.
Test Bed
Two 2800-series routers were connected with a back-to-back serial link, one of them generating the clock. PPP encapsulation was used on the serial link. A traffic-generating node was connected to the Ethernet port of one of the routers to generate the background load. IP SLA using ICMP echo packets was started on the same router to measure response time and jitter of a simple request-response application (ICMP ping).
Router Configurations
Minimum router configurations were used with no dynamic routing. The relevant parts of router configurations are displayed below:
Configuration of the IP SLA originating router
hostname a1 ! ip cef ! class-map match-all Echo match protocol icmp ! policy-map EchoPriority class Echo priority 64 class class-default fair-queue ! interface FastEthernet0/0 ip address 10.0.0.5 255.255.255.0 ! interface Serial0/1/0 bandwidth 512 ip address 172.16.1.129 255.255.255.252 encapsulation ppp load-interval 30 service-policy output EchoPriority ! end The second router has an almost identical configuration (with different IP addresses).
Load Generation
UDP flooding implemented in PERL was used to generate the background load and saturate the WAN interface. Two sets of measurements were performed. In the first test, a continuous flood of constantly-spaced fixed-size packets sent to a single UDP port was generated (similar to constant bit rate traffic). This traffic stream generated a single conversation in the fair queuing model used on the WAN interface.
Cisco IOS uses fair queuing as soon as a service policy including a queuing action is configured on an interface.
The second test flooded the WAN link with variable-sized packets sent at a fixed interval to random destination UDP ports. The generated bandwidth varied widely due to random packet sizes and the traffic stream generated hundreds of conversations in the fair queuing structure. In both cases, the CPU utilization was measured on a1 and a2 to verify that the CPU load does not increase 50% (high CPU load could impact the jitter measurements).
a1#show proc cpu | inc CPU CPU utilization for five seconds: 8%/6%; one minute: 8%; five minutes: 5% a2#sh proc cpu | inc CPU CPU utilization for five seconds: 20%/10%; one minute: 12%; five minutes: 8% Response Time and Jitter Measurement
An IP SLA probe was configured on one of the routers generating small ICMP ECHO packets that were sent over the WAN link. The ICMP traffic is classified as priority traffic in the service policy attached to the WAN interface ensuring that the ICMP packets enter the hardware queue prior to any packets generated by the UDP flood. The measured delay and jitter is thus solely the result of the hardware queue between the software fair queuing structures and the interface hardware.
ip sla 50000 icmp-jitter 172.16.1.130 timeout 1000 threshold 500 frequency 2 history hours-of-statistics-kept 1 history distributions-of-statistics-kept 2 The IP SLA probe was started after the test load has reached a steady state (saturated WAN interface) and the aggregated SLA statistics were inspected while the load was still present. The show ip sla statistics aggregated command was used to inspect the statistics and the RTT and source-to-destination jitter values were collected
a1#show ip sla statistics aggregated Round Trip Time (RTT) for Index 50000 Start Time Index: 13:15:22.851 UTC Fri Apr 18 2008 Type of operation: icmpJitter RTT Values: Number Of RTT: 387 RTT Min/Avg/Max: 6/15/31 Latency one-way time: Number of Latency one-way Samples: 0 Source to Destination Latency one way Min/Avg/Max: 0/0/0 Destination to Source Latency one way Min/Avg/Max: 0/0/0 Jitter Time: Number of Jitter Samples: 334 Source to Destination Jitter Min/Avg/Max: 1/6/23 Destination to Source Jitter Min/Avg/Max: 1/1/1 Test Results
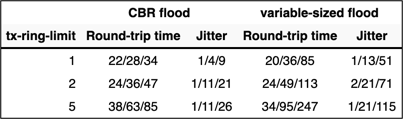
The tests were performed at line speeds of 128 and 512 kbps with different tx-ring-limit settings. The tx-ring-limit values were changed at both ends of the WAN link. The test result values are triplets: minimum, average and maximum measured value as reported by IP SLA. 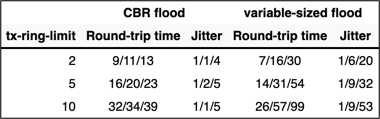
This article written by Ivan Pepelnjak in early 2000s was originally published on CT3 wiki which became unreachable in 2019. The text was retrieved from an Internet Archive snapshot, updated, and republished on ipSpace.net.
Understanding and Tuning the tx-ring-limit Value
The documentation set for this product strives to use bias-free language. For the purposes of this documentation set, bias-free is defined as language that does not imply discrimination based on age, disability, gender, racial identity, ethnic identity, sexual orientation, socioeconomic status, and intersectionality. Exceptions may be present in the documentation due to language that is hardcoded in the user interfaces of the product software, language used based on RFP documentation, or language that is used by a referenced third-party product. Learn more about how Cisco is using Inclusive Language.
Contents
Introduction
This document discusses the function of a hardware transmit ring and the purpose of the tx-ring-limit command on ATM router interface hardware that supports per-virtual circuit (VC) queueing. Cisco router interfaces configured with service policies store packets for an ATM VC in one of two sets of queues depending on the congestion level of the VC:
| Queue | Location | Queueing Methods | Service Policies Apply | Command to Tune |
|---|---|---|---|---|
| Hardware queue or transmit ring | Port adapter or network module | FIFO only | No | tx-ring-limit |
| Layer-3 queue | Layer-3 processor system or interface buffers | N/A | Yes | Varies with queueing method: — vc-hold-queue — queue-limit |
Prerequisites
Requirements
There are no specific requirements for this document.
Components Used
This document is not restricted to specific software and hardware versions.
Conventions
Refer to Cisco Technical Tips Conventions for more information on document conventions.
Understanding Particles
Before discussing the transmit ring, we first need to understand what a particle is. A particle forms the basic building block of packet buffering on many platforms, including the Cisco 7200 router series and the versatile interface processor (VIP) on the Cisco 7500 router series. Depending on the packet length, Cisco IOS® software uses one or more particles to store a packet. Let’s look at an example. When receiving a 1200-byte packet, IOS retrieves the next free particle and copies the packet data into the particle. When the first particle is filled, IOS moves to the next free particle, links it to the first particle, and continues copying the data into this second particle. Upon completion, the 1200 bytes of the packet are stored in three discontiguous pieces of memory that IOS logically makes a part of a single packet buffers. IOS particle size varies from platform to platform. All particles within a given pool are the same size. This uniformity simplifies the particle management algorithms and helps contribute to efficient memory use.
Understanding Buffer Rings
Along with public and private interface pools, Cisco IOS creates special buffer control structures called rings. Cisco IOS and interface controllers use these rings to control which buffers are used to receive and transmit packets to the media. The rings themselves consist of media-controller-specific elements that point to individual packet buffers elsewhere in I/O memory. Each interface has a pair of rings — a receive ring for receiving packets and a transmit ring for transmitting packets. The size of the rings can vary with the interface controller. In general, the size of the transmit ring is based on bandwidth of the interface or VC and is a power of two (Cisco Bug ID CSCdk17210).
| Interface | Rings | |||||
|---|---|---|---|---|---|---|
| Line Rate(Mb/s) | 2 | 10 | 20 | 30 | 40 | . |
| txcount | 2 | 4 | 8 | 16 | 32 | 64 |
Note: On the 7200 series platform, the transmit ring packet buffers come from the receive ring of the originating interface for a switched packet or from a public pool if the packet was originated by IOS. They are deallocated from the transmit ring and returned to their original pool after the payload data is transmitted.
PA-A3 Architecture Overview
To ensure high forwarding performance, the PA-A3 port adapter uses separate receive and transmit segmentation and reassembly (SAR) chips. Each SAR is supported by its own subsystem of onboard memory to store packets as well as key data structures like the VC table. This memory specifically includes 4 MB of SDRAM, which is chunked into particles. The following table illustrates the number and size of particles on the receive and transmit paths on the PA-A3.
| Ring | Particle Size | Number of Particles |
|---|---|---|
| Receive Ring | 288 bytes | n/a |
| Transmit Ring | 576* bytes | 6000 (144 particles are reserved) |
* The transmit ring’s particle size also is described as being 580 bytes. This value includes the 4-byte ATM core header that travels with the packet inside the router. The sizes in the above table were selected because they are divisible by 48 (the size of a cell’s payload field) and by the cache line size (32 bytes) for maximum performance. They are designed to prevent the SAR from introducing inter-buffer delay when a packet requires multiple buffers. The transmit particle size of 576 bytes also was selected to cover about 90 percent of Internet packets.
Transmit Ring Allocation Scheme on the PA-A3
The PA-A3 driver assigns a default transmit-ring value to each VC. This value varies with the ATM service category assigned to the VC. The following table lists the default values.
| VC Service Category | PA-A3-OC3, T3, E3 Default Transmit Ring Value | PA-A3-IMA Default Transmit Ring Value | PA-A3-OC12 Default Transmit Ring Value | Time of Enforcement |
|---|---|---|---|---|
| VBR-nrt | Based on formula**: (48 x SCR) / (Particle_size x 5) Minimum value is 40, and overrides any calculated value less than 40 with a very low SCR. Note: SCR is the cell rate with ATM overhead included. | Based on formula: (48 x SCR) / (Particle_size x 5) Minimum value is 40, and overrides any calculated value less than 40 with a very low SCR. Note: SCR is the cell rate with ATM overhead included. | Based on the following formula: Average rate (SCR) * 2 * TOTAL_CREDITS / VISIBLE_BANDWIDTH TOTAL_CREDITS = 8192 VISIBLE_BANDWIDTH = 599040 Note: If this formula calculates a value which is less than the default of 128, then the VC’s transmit ring limit is set to 128. | Always |
| ABR | 128 | 128 | N/A | Always* |
| UBR | 40 | 128 | 128 | Only when total credit utilization exceeds 75 percent or the tx_threshold value, as shown in show controller atm. |
* Originally, the PA-A3-OC12 did not implement always-active limiting of VBR-nrt PVCs to the current transmit ring value. Bug ID CSCdx11084 resolves this issue. . ** SCR should be expressed in cells/sec.
Displaying the Current Transmit Ring Values
Originally, the value of the transmit ring was only visible via a hidden command. The show atm vc command now displays the current value. You also can use the debug atm events command to view the VC setup messages between the PA-A3 driver and the host CPU. The following sets of output were captured on a PA-A3 in a 7200 series router. The transmit ring value is displayed as the tx_limit value, which implements the particle buffer quota allocated for a specific VC in the transmit direction. PVC 1/100 is configured as VBR-nrt. Based on an SCR of 3500 kbps, the PA-A3 assigns a tx_limit of 137. To see how this calculation is made, we need to convert an SCR of 3500 kbps to cells/sec. Notice that (3,500,000 bits /sec) * (1 byte / 8 bits) * (1 cell / 53 byes ) = (3, 500, 000 cells) / (8 * 53 sec) = 8254 cells / sec. Once we have the SCR value in cells / sec, we can apply the formula above to ger tx_limit = 137.
7200-17(config)#interface atm 4/0 7200-17(config-if)#pvc 1/100 7200-17(config-if-atm-vc)#vbr-nrt 4000 3500 94 7200-17(config-if-atm-vc)# *Oct 14 17:56:06.886: Reserved bw for 1/100 Available bw = 141500 7200-17(config-if-atm-vc)#exit 7200-17(config-if)#logging *Oct 14 17:56:16.370: atmdx_setup_vc(ATM4/0): vc:6 vpi:1 vci:100 state:2 config_status:0 *Oct 14 17:56:16.370: atmdx_setup_cos(ATM4/0): vc:6 wred_name:- max_q:0 *Oct 14 17:56:16.370: atmdx_pas_vc_setup(ATM4/0): vcd 6, atm hdr 0x00100640, mtu 4482 *Oct 14 17:56:16.370: VBR: pcr 9433, scr 8254, mbs 94 *Oct 14 17:56:16.370: vc tx_limit=137, rx_limit=47 *Oct 14 17:56:16.374: Created 64-bit VC count
PVC 1/101 is configured as ABR. The PA-A3 assigns the default ABR tx_limit value of 128. (See the table above.)
7200-17(config-if)#pvc 1/102 7200-17(config-if-atm-vc)#abr ? Peak Cell Rate(PCR) in Kbps rate-factors Specify rate increase and rate decrease factors (inverse) 7200-17(config-if-atm-vc)#abr 4000 1000 7200-17(config-if-atm-vc)# *Oct 14 17:57:45.066: Reserved bw for 1/102 Available bw = 140500 *Oct 14 18:00:11.662: atmdx_setup_vc(ATM4/0): vc:8 vpi:1 vci:102 state:2 config_status:0 *Oct 14 18:00:11.662: atmdx_setup_cos(ATM4/0): vc:8 wred_name:- max_q:0 *Oct 14 18:00:11.662: atmdx_pas_vc_setup(ATM4/0): vcd 8, atm hdr 0x00100660, mtu 4482 *Oct 14 18:00:11.662: ABR: pcr 9433, mcr 2358, icr 9433 *Oct 14 18:00:11.662: vc tx_limit=128, rx_limit=47 *Oct 14 18:00:11.666: Created 64-bit VC counters
PVC 1/102 is configured as UBR. The PA-A3 assigns the default UBR tx_limit value of 40. (See the table above.)
7200-17(config-if)#pvc 1/101 7200-17(config-if-atm-vc)#ubr 10000 7200-17(config-if-atm-vc)# *Oct 14 17:56:49.466: Reserved bw for 1/101 Available bw = 141500 *Oct 14 17:57:03.734: atmdx_setup_vc(ATM4/0): vc:7 vpi:1 vci:101 state:2 config_status:0 *Oct 14 17:57:03.734: atmdx_setup_cos(ATM4/0): vc:7 wred_name:- max_q:0 *Oct 14 17:57:03.734: atmdx_pas_vc_setup(ATM4/0): vcd 7, atm hdr 0x00100650, mtu 4482 *Oct 14 17:57:03.734: UBR: pcr 23584 *Oct 14 17:57:03.734: vc tx_limit=40, rx_limit=117 *Oct 14 17:57:03.738: Created 64-bit VC counters
- Individual quota on each VBR-nrt and ABR VC — Compares each VC’s tx_count and tx_limit values. It discards subsequent packets when the tx_count is greater than the tx_limit on any one VC. It is important to note that a burst of packets can exceed the transmit ring of a VBR-nrt VC at an instant in time and lead to output drops.
- Overall quota — Considers the tx_threshold value. The PA-A3 allows for larger bursts on UBR VCs by enforcing traffic policing on such VCs only when the total packet buffer usage on the PA-A3 reaches this preset threshold.
Note: If a packet requires multiple particles and the transmit ring is full, the PA-A3 allows a VC to exceed its quota if particles are available. This scheme is designed to accommodate a small burst of packets without output drops.
The show controller atm command displays several counters relevant to transmit credits.
7200-17#show controller atm 4/0 Interface ATM4/0 is up Hardware is ENHANCED ATM PA - OC3 (155000Kbps) Framer is PMC PM5346 S/UNI-155-LITE, SAR is LSI ATMIZER II Firmware rev: G125, Framer rev: 0, ATMIZER II rev: 3 idb=0x622105EC, ds=0x62217DE0, vc=0x62246A00 slot 4, unit 9, subunit 0, fci_type 0x0059, ticks 190386 1200 rx buffers: size=512, encap=64, trailer=28, magic=4 Curr Stats: VCC count: current=7, peak=7 SAR crashes: Rx SAR=0, Tx SAR=0 rx_cell_lost=0, rx_no_buffer=0, rx_crc_10=0 rx_cell_len=0, rx_no_vcd=0, rx_cell_throttle=0, tx_aci_err=0 Rx Free Ring status: base=0x3E26E040, size=2048, write=176 Rx Compl Ring status: base=0x7B162E60, size=2048, read=1200 Tx Ring status: base=0x3E713540, size=8192, write=2157 Tx Compl Ring status: base=0x4B166EA0, size=4096, read=1078 BFD Cache status: base=0x62240980, size=6144, read=6142 Rx Cache status: base=0x62237E80, size=16, write=0 Tx Shadow status: base=0x62238900, size=8192, read=2143, write=2157 Control data: rx_max_spins=3, max_tx_count=17, tx_count=14 rx_threshold=800, rx_count=0, tx_threshold=4608 tx bfd write indx=0x4, rx_pool_info=0x62237F20
The following table describes the values used by the PA-A3 to enforce the overall transmit credit scheme:
| Value | Description |
|---|---|
| max_tx_count | Histogram of the maximum number of transmit particles ever held by the PA-A3 microcode. |
| tx_count | Total number of transmit particles currently being held by the PA-A3 microcode. |
Note: The PA-A3 microcode also tracks the tx_count of each VC. When a particle is sent to the PA-A3 microcode from the PA-A3 driver, the tx_count increments by one.
When Should the Transmit Ring Be Tuned?
The transmit ring serves as a staging area for packets in line to be transmitted. The router needs to enqueue a sufficient number of packets on the transmit ring and ensure that the interface driver has packets with which to fill available cell timeslots.
Originally, the PA-A3 driver did not adjust the transmit ring size when a service policy with low latency queueing (LLQ) was applied. With current images, the PA-A3 tunes down the value from the above defaults (Cisco Bug ID CSCds63407) to minimize queueing-related delay.
The primary reason to tune the transmit ring is to reduce latency caused by queueing. When tuning the transmit ring, consider the following:
- On any network interface, queueing forces a choice between latency and the amount of burst that the interface can sustain. Larger queue sizes sustain longer bursts while increasing delay. Tune the size of a queue when you feel the VC’s traffic is experiencing unnecessary delay.
- Consider the packet size. Configure a tx-ring-limit value that accommodates four packets. For example, if your packets are 1500 bytes, set a tx-ring-limit value of 16 = (4 packets) * (4 particles).
- Ensure the transmit credit is large enough to support one MTU-sized packet and/or the number of cells equal to the maximum burst size (MBS) for a VBR-nrt PVC.
- Configure a low value with low-bandwidth VCs, such as a 128 kbps SCR. For example, on a low-speed VC with an SCR of 160 kbps, a tx-ring-limit of ten is relatively high and can lead to significant latency (for example, hundreds of milliseconds) in the driver-level queue. Tune the tx-ring-limit down to its minimum value in this configuration.
- Configure higher values for high-speed VCs. Selecting a value of less than four may inhibit the VC from transmitting at its configured rate if the PA-A3 implements back pressure too aggressively and the transmit ring does not have a ready supply of packets waiting to be transmitted. Ensure that a low value does not affect VC throughput. (See Cisco Bug ID CSCdk17210.)
In other words, the size of the transmit ring needs to be small enough to avoid introducing latency due to queueing, and it needs to be large enough to avoid drops and a resulting impact to TCP-based flows.
An interface first removes the packets from the layer-3 queueing system and then queues them on the transmit ring. Service policies apply only to packets in the layer-3 queues and are transparent to the transmit ring.
Queueing on the transmit ring introduces a serialization delay that is directly proportional to the depth of the ring. An excessive serialization delay can impact latency budgets for delay-sensitive applications such as voice. Thus, Cisco recommends reducing the size of the transmit ring for VCs carrying voice. Select a value based on the amount of amount of serialization delay, expressed in seconds, introduced by the transmit ring. Use the following formula:
((P*8)*D)/S P = Packet size in bytes. Multiply by eight to convert to bits. D = Transmit-ring depth. S = Speed of the VC in bps.
Note: IP packets on the Internet are typically one of three sizes: 64 bytes (for example, control messages), 1500 bytes (for example, file transfers), or 256 bytes (all other traffic). These values produce a typical overall Internet packet size of 250 bytes.
Note: The following table summarizes the advantages and disadvantages of larger or smaller transmit ring sizes:
| Size of Transmit Ring | Advantage | Disadvantage |
|---|---|---|
| High Value | Recommended for data VCs to accommodate bursts. | Not recommended for voice VCs. Can introduce increased latency and jitter. |
| Low Value | Recommended for voice VCs to reduce delay due to queueing and jitter. | Not recommended for relatively high-speed VCs. Can introduce reduced throughput if tuned to such a low value that no packets are ready to be sent once the wire is free. |
Use the tx-ring-limit command in VC configuration mode to tune the size of the transmit ring.
7200-1(config-subif)#pvc 2/2 7200-1(config-if-atm-vc)#? ATM virtual circuit configuration commands: abr Enter Available Bit Rate (pcr)(mcr) broadcast Pseudo-broadcast class-vc Configure default vc-class name default Set a command to its defaults encapsulation Select ATM Encapsulation for VC exit-vc Exit from ATM VC configuration mode ilmi Configure ILMI management inarp Change the inverse arp timer on the PVC no Negate a command or set its defaults oam Configure oam parameters oam-pvc Send oam cells on this pvc protocol Map an upper layer protocol to this connection. random-detect Configure WRED service-policy Attach a policy-map to a VC transmit-priority set the transmit priority for this VC tx-ring-limit Configure PA level transmit ring limit ubr Enter Unspecified Peak Cell Rate (pcr) in Kbps. vbr-nrt Enter Variable Bit Rate (pcr)(scr)(bcs) 7200-1(config-if-atm-vc)#tx-ring-limit ? 3-6000> Number (ring limit)
Use the show atm vc command to display the currently configured value.
7200-1#show atm vc VC 3 doesn't exist on interface ATM3/0 ATM5/0.2: VCD: 3, VPI: 2, VCI: 2 VBR-NRT, PeakRate: 30000, Average Rate: 20000, Burst Cells: 94 AAL5-LLC/SNAP, etype:0x0, Flags: 0x20, VCmode: 0x0 OAM frequency: 0 second(s) PA TxRingLimit: 10 InARP frequency: 15 minutes(s) Transmit priority 2 InPkts: 0, OutPkts: 0, InBytes: 0, OutBytes: 0 InPRoc: 0, OutPRoc: 0 InFast: 0, OutFast: 0, InAS: 0, OutAS: 0 InPktDrops: 0, OutPktDrops: 0 CrcErrors: 0, SarTimeOuts: 0, OverSizedSDUs: 0 OAM cells received: 0 OAM cells sent: 0 Status: UP
In addition, use the show atm pvc vpi/vci command to view both the current transmit and receive ring limits. The following output was captured on a 7200 Series router running Cisco IOS Software Release 12.2(10).
viking#show atm pvc 1/101 ATM6/0: VCD: 2, VPI: 1, VCI: 101 UBR, PeakRate: 149760 AAL5-LLC/SNAP, etype:0x0, Flags: 0xC20, VCmode: 0x0 OAM frequency: 0 second(s), OAM retry frequency: 1 second(s), OAM retry frequency: 1 second(s) OAM up retry count: 3, OAM down retry count: 5 OAM Loopback status: OAM Disabled OAM VC state: Not Managed ILMI VC state: Not Managed VC TxRingLimit: 40 particles VC Rx Limit: 800 particles
Impact of Very Small tx-ring-limit Values
On the transmit path, the host CPU transfers the payload from the host buffers to the local particle buffers on the PA-A3. The firmware running on the PA-A3 caches several buffer descriptors and frees them in a group. During the caching period, the PA-A3 does not accept new packets even though the contents of the local memory have been transmitted on the physical wire. The purpose of this scheme is to optimize overall performance. Thus, when configuring a non-default tx-ring-limit value, consider the buffer descriptor return delay.
In addition, if you configure a tx-ring-limit value of one with given a particle size of 576 bytes, a 1500-byte packet is removed from the queue as follows:
- The PA-A3 driver queues the first particle in the transmit ring, and remembers that this packet is stored in two other memory particles.
- During the next time that the transmit ring is empty, the second particle of the packet is put in the transmit ring.
- During the next time that the transmit ring is empty again, the third particle is put in the transmit ring.
Even though the transmit ring consists of only one 576 byte particle, MTU/port-speed is still the worst-case latency through the transmit ring.
Known Issues
When the tx-ring-limit command is applied to a VC through a vc-class statement, the PA-A3 does not apply the configured value. Confirm this result by displaying the current value in the show atm vc detail command. Tuning the transmit ring using a vc-class was implemented in Cisco IOS Software Release 12.1 (Cisco Bug ID CSCdm93064). CSCdv59010 resolves a problem with the tx-ring-limit in certain versions of Cisco IOS Software Release 12.2. When you apply the tx-ring-limit command through the vc-class statement to an ATM PVC, the transmit ring size is not modified. Confirm this result using the show atm vc detail command, after applying the command through the vc-class and class-vc command pairs.
When added to a PVC on a PA-A3 in a Cisco 7200 series router running Cisco IOS Software Release 12.2(1), the tx-ring-limit command is duplicated, as shown below (Cisco Bug ID CSCdu19350).
interface ATM1/0.1 point-to-point description dlci-101, cr3640 ip unnumbered Loopback0 pvc 0/101 tx-ring-limit 3 tx-ring-limit 3
The condition is harmless and does not affect the operation of the router.
Cisco bug ID CSCdv71623 resolves a problem with output drops on a multilink PPP bundle interface when the traffic rate is well below the line rate. This problem was seen in CSCdv89201 on an ATM interface with a tx-ring-limit value greater than five. The problem becomes particularly apparent when fragmentation is disabled or when the link weights (fragment size limits) are large — common on higher speed links like T1s or E1s — and the data traffic consists of a mix of small and large packets. Enabling fragmentation and using a small fragment size (set by the interface configuration command ppp multilink fragment delay) improves operation significantly. However, you should verify that your router has sufficient processing capacity to support these high levels of fragmentation without overloading the system CPU, before using this as a workaround.
Cisco bug ID CSCdw29890 resolves a problem with the tx-ring-limit command being accepted by the CLI for ATM PVC bundles, but not taking effect. However, you do not normally need to change the tx-ring-limit on ATM PVC bundles. The reason is that, reducing the ring size effectively moves all the transmit buffering to a QoS-controlled queue, so an arriving priority packet is transmitted immediately to minimize delay on low-speed interfaces. With ATM PVC bundles, cells from packets of all the member VCs are always sent simultaneously (and interleaved), so the delay is minimized automatically.
Tuning the tx-ring-limit on 3600 and 2600 Routers
Current Cisco IOS software images support tuning the transmit ring on the ATM network modules for Cisco 2600 and 3600 series routers (Cisco Bug ID CSCdt73385). The current value appears in the show atm vc output.
Related Information
- More ATM Information
- Tools and Resources — Cisco Systems
- Technical Support & Documentation — Cisco Systems
Курс Cisco CCNA-IACS 1.0
Основы администрирования решений на базе оборудования Cisco Systems (Implementing and Administering Cisco Solutions — ранее назывался Interconnecting Cisco Network Devices)
Даты ближайших онлайн-курсов
- В данный момент в расписании нет ближайших занятий. Возможно индивидуальное обучение — оставьте нам запрос на курс — мы обязательно ответим и уточним детали.
Краткое описание курса CCNA-IACS (версия CCNA-IACS 1.0)
Курс CCNA (он же CCNAv2, он же ранее CCNA Next, он же IACS 1.0) — это долгожданное обновление базовых курсов Cisco. В предыдущей итерации, изменяя древо сертификаций фирма Cisco наделала много разных подвидов CCNA — как достаточно толковые CCNA:Security и CCNA:Service Provider, так и экзотичные в плане востребованности на рынке труда CCNA:Cloud и CCNA:Industrial. На этом витке развития принято решение вернуться к «одному главному азбучному курсу молодого бойца» — теперь он называется Implementing and Administering Cisco Solutions, но для простоты его назвали так же, как и сертификацию — CCNA.
В курсе изучается примерно то же самое, что ранее было в ICND1 и ICND2 (подробнее про различия можно посмотреть на нашем бесплатно доступном вебинаре), с добавлением тем по безопасности, углублению модулей про WiFi и QoS, а также серьёзному расширению материала по SD-WAN и автоматизации работы сетей (не только WAN, но и всех вообще).
Отдельно хочется добавить про формат преподавания — подробное объяснение «почему у вас курс такой долгий, а он должен пять дней быть» находится вот в этой новости. Проблема, вкратце, в том, что если до 2020 года курсы для базовых сертификаций Cisco готовили к экзамену на ~80% (т.е. все равно требовался доп.материал, на экзаменах были вопросы про то, что физически отсутствует в материале авторизованных курсов — поэтому мы делали дополнительные занятия в Advanced CCNA), то теперь фирмой Cisco совершенно официально пишется, что материал курса — это занятия с преподавателем плюс самостоятельные, и есть целые блоки тем, которые предлагается изучать вне класса. При этом данные темы заявлены в материале курса, что дополнительно путает студентов. Мы читаем CCNA в полноценном формате, т.е. практики и обсуждения есть у всех тем, и они проходят в рамках курса, а не отложены на самостоятельную проработку — поэтому продолжительность занятий увеличивается.
Мы углубляем материал наших курсов, добавляя практические работы, заменяя демонстрации на лабораторные работы, рассказывая дополнительные темы — поэтому наш курс CCNA-IACS 1.0 лучше подходит для подготовки к экзаменам, чем стандартный «минималистичный» авторизованный CCNA-IACS.
Ruslan V. Karmanov
Лабораторный стенд
- Cisco IOU Router (adventerprisek9 15.7)
- Cisco IOU Switch (adventerprisek9 15.2)
- Virtual PC
- Cisco Wireless LAN Controller 8.10
- Windows Server 2019 Datacenter
Версии ПО могут быть более новыми, чем указаны в списке. В случае windows/linux на ОС обычно установлены последние обновления.
Нужен для получения статусов
- Сертификация CCNA — Cisco Certified Network Associate (CCNA) v2
Подготавливает к сдаче сертификационных экзаменов
- Экзамен 200-301 — записаться на вебинар по проработке вопросов экзамена
Программа курса CCNA-IACS 1.0
Модуль 1 — Основы сетевых технологий
- What Is a Computer Network?
- Components of a Network
- Characteristics of a Network
- Physical vs. Logical Topologies
- Interpreting a Network Diagram
- Impact of User Applications on the Network
Модуль 2 — Introducing the Host-To-Host Communications Model
- Host-To-Host Communications Overview
- ISO OSI Reference Model
- TCP/IP Protocol Suite
- Peer-To-Peer Communications
- Encapsulation and De-Encapsulation
- TCP/IP Stack vs OSI Reference Model
Модуль 3 — Operating Cisco IOS Software
- Cisco IOS Software Features and Functions
- Cisco IOS Software CLI Functions
- Cisco IOS Software Modes
- Get Started with Cisco CLI
Модуль 4 — Introducing LANs
- Introduction
- Local Area Networks
- LAN Components
- Need for Switches
- Characteristics and Features of Switches
Модуль 5 — Exploring the TCP/IP Link Layer
- Ethernet LAN Connection Media
- Ethernet Frame Structure
- LAN Communication Types
- MAC Addresses
- Frame Switching
- Observe How a Switch Operates
- Duplex Communication
Модуль 6 — Starting a Switch
- Switch Installation
- Connecting to a Console Port
- Switch LED Indicators
- Basic show Commands and Information
- Perform Basic Switch Configuration
- Implement the Initial Switch Configuration
Модуль 7 — Introducing the TCP/IP Internet Layer, IPv4 Addressing, and Subnets
- Internet Protocol
- Decimal and Binary Number Systems
- Binary-to-Decimal Conversion
- Decimal-to-Binary Conversion
- IPv4 Address Representation
- IPv4 Header Fields
- IPv4 Address Classes
- Subnet Masks
- Subnets
- Implementing Subnetting: Borrowing Bits
- Implementing Subnetting: Determining the Addressing Scheme
- Benefits of VLSM and Implementing VLSM
- Private vs. Public IPv4 Addresses
- Reserved IPv4 Addresses
- Verifying IPv4 Address of a Host
Модуль 8 — Explaining the TCP/IP Transport Layer and Application Layer
- TCP/IP Transport Layer Functions
- Reliable vs. Best-Effort Transport
- TCP Characteristics
- UDP Characteristics
- TCP/IP Application Layer
- Introducing HTTP
- Domain Name System
- Explaining DHCP for IPv4
- Inspect TCP/IP Applications
Модуль 9 — Exploring the Functions of Routing
- Role of a Router
- Router Components
- Router Functions
- Routing Table
- Path Determination
Модуль 10 — Configuring a Cisco Router
- Initial Router Setup
- Configuring Router Interfaces
- Configuring IPv4 Addresses on Router Interfaces
- Checking Interface Configuration and Status
- Configure an Interface on a Cisco Router
- Exploring Connected Devices
- Using Cisco Discovery Protocol
- Configure and Verify LLDP
- Configure and Verify Layer 2 Discovery Protocols
- Implement an Initial Router Configuration
Модуль 11 — Exploring the Packet Delivery Process
- Layer 2 Addressing
- Layer 3 Addressing
- Default Gateways
- Address Resolution Protocol
- Configure Default Gateway
- Host-To-Host Packet Delivery
- Explore Packet Forwarding
Модуль 12 — Troubleshooting a Simple Network
- Troubleshooting Methods
- Troubleshooting Tools
- Troubleshooting Common Switch Media Issues
- Troubleshooting Common Switch Port Issues
- Troubleshoot Switch Media and Port Issues
- Troubleshoot Port Duplex Issues
- Troubleshooting Common Problems Associated with IPv4 Addressing
Модуль 13 — Introducing Basic IPv6
- IPv4 Address Exhaustion Workarounds
- IPv6 Features
- IPv6 Addresses and Address Types
- Comparison of IPv4 and IPv6 Headers
- Internet Control Message Protocol Version 6
- Neighbor Discovery
- IPv6 Address Allocation
- Configure Basic IPv6 Connectivity
- Verification of End-To-End IPv6 Connectivity
Модуль 14 — Configuring Static Routing
- Routing Operation
- Static and Dynamic Routing Comparison
- When to Use Static Routing
- IPv4 Static Route Configuration
- Default Routes
- Verifying Static and Default Route Configuration
- Configure and Verify IPv4 Static Routes
- Configuring IPv6 Static Routes
- Configure IPv6 Static Routes
- Implement IPv4 Static Routing
- Implement IPv6 Static Routing
Модуль 15 — Implementing VLANs and Trunks
- VLAN Introduction
- Creating a VLAN
- Assigning a Port to a VLAN
- Trunking with 802.1Q
- Configuring an 802.1Q Trunk
- Configure VLAN and Trunk
- VLAN Design Considerations
- Troubleshoot VLANs and Trunk
Модуль 16 — Routing Between VLANs
- Purpose of Inter-VLAN Routing
- Options for Inter-VLAN Routing
- Configure a Router on a Stick
- Implement Multiple VLANs and Basic Routing Between the VLANs
Модуль 17 — Introducing OSPF
- Dynamic Routing Protocols
- Path Selection
- Link-State Routing Protocol Overview
- Link-State Routing Protocol Data Structures
- Introducing OSPF
- Establishing OSPF Neighbor Adjacencies
- OSPF Neighbor States
- SPF Algorithm
- Building a Link-State Database
- Configure and Verify Single-Area OSPF
- Routing for IPv6
Модуль 18 — Building Redundant Switched Topologies
- Physical Redundancy in a LAN
- Issues in Redundant Topologies
- Spanning Tree Operation
- Types of Spanning Tree Protocols
- PortFast and BPDU Guard
- Rapid Spanning Tree Protocol
Модуль 19 — Improving Redundant Switched Topologies with EtherChannel
- EtherChannel Overview
- EtherChannel Configuration Options
- Configuring and Verifying EtherChannel
- Configure and Verify EtherChannel
- Improve Redundant Switched Topologies with EtherChannel
Модуль 20 — Exploring Layer 3 Redundancy
- Need for Default Gateway Redundancy
- Understanding FHRP
- Understanding HSRP
Модуль 21 — Introducing WAN Technologies
- Introduction to WAN Technologies
- WAN Devices and Demarcation Point
- WAN Topology Options
- WAN Connectivity Options
- Virtual Private Networks
- Enterprise-Managed VPNs
- Provider-Managed VPNs
Модуль 22 — Explaining Basics of ACL
- ACL Overview
- ACL Operation
- ACL Wildcard Masking
- Wildcard Mask Abbreviations
- Types of Basic ACLs
- Configuring Standard IPv4 ACLs
- Configuring Extended IPv4 ACLs
- Verifying and Modifying IPv4 ACLs
- Applying IPv4 ACLs to Filter Network Traffic
- Configure and Verify IPv4 ACLs
- Implement Numbered and Named IPv4 ACLs
Модуль 23 — Enabling Internet Connectivity
- Configure a Provider-Assigned IPv4 Address
- Introducing Network Address Translation
- NAT Terminology and Translation Mechanisms
- Benefits and Drawbacks of NAT
- Static NAT and Port Forwarding
- Dynamic NAT
- Port Address Translation
- Configuring and Verifying Inside IPv4 NAT
- Configure Static NAT
- Configure Dynamic NAT and PAT
- Implement PAT
Модуль 24 — Основы QoS
Материал вебинара Advanced CCNA — Основы QoS, в частности:
Модуль 1 — Теоретические основы управления качеством сервиса в сетях (QoS)
- Типы трафика и причины, по которым не всегда хорошо обрабатывать все пакеты идентично. QoS и управление bandwidth, delay, jitter и packet loss.
- Механизмы QoS — маркировка трафика. CoS 802.1p (нормальный PCP и короткий) и ToS / TC. Варианты — IP precedence с Class Selector (CS) и DSCP.
- Механизмы QoS — классификация трафика. От простого к сложному — MLS, ACL, Network Based Application Recognition (NBAR), NBAR2. Режимы NBAR Active Mode и Passive Mode. Расширяем NBAR — правила PDLM и подгрузка Protocol Pack Library.
- Управление заторами, очередями и перегрузками (Congestion Management). Основные варианты — CBWFQ, LLQ, PQ, CQ, WFQ.
- Механизмы QoS — разгрузка очередей (scheduling). Механизмы scheduling strict priority, round-robin и weighted fair.
- Механизмы QoS — Congestion Avoidance; схема tail drop и выборочного сброса WRED. Проблема глобальной синхронизации TCP.
- Механизмы QoS — policing и shaping.
- QoS Domain и Trust boundary. Граница trusted/untrusted domain у организаций и операторов связи. Реализация концепции End-to-End QoS Enterprise Design.
Модуль 2 — Канальный уровень
- Способы LAN-коммутации: store-and-forward (и использование Header Data Split), быстрые cut-through и fragment-free
- Буферизация на интерфейсе. Управление буферизацией — tx-ring и tx-ring-limit / tx-queue-limit. Настройка hold-queue. Работа fair-queue.
- Простой flow control — 802.3x. Включение на портах в IOS / NX-OS / IOS XR.
- Технологии Link Fragmentation и Interleaving на примере serial link.
- WiFi: 802.11e и Wireless Multimedia Extensions (WMM). Сравнение приоритетов 802.1p и AC у 802.11e. Изменение CSMA/CA с NoAck и TID.
Модуль 25 — Explaining Wireless Fundamentals
- Wireless Technologies
- WLAN Architectures
- WiFi Channels
- AP and WLC Management
- Log into the WLC
- Monitor the WLC
- Configure a Dynamic (VLAN) Interface
- Configure a DHCP Scope
- Configure a WLAN
- Define a RADIUS Server
- Explore Management Options
Модуль 26 — Introducing Architectures and Virtualization
- Introduction to Network Design
- Enterprise Three-Tier Hierarchical Network Design
- Spine-Leaf Network Design
- Cisco Enterprise Architecture Model
- Cloud Computing Overview
- Network Device Architecture
- Virtualization Fundamentals
Модуль 27 — Explaining the Evolution of Intelligent Networks
- Overview of Network Programmability in Enterprise Networks
- Software-Defined Networking
- Common Programmability Protocols and Methods
- Configuration Management Tools
- Introducing Cisco DNA Center
- Explore the Cisco DNA Center
- Introducing Cisco SD-Access
- Introducing Cisco SD-WAN
Модуль 28 — Introducing System Monitoring
- Introduction
- Introducing Syslog
- Syslog Message Format
- SNMP Overview
- Enabling Network Time Protocol
- Configure and Verify NTP
- Configure System Message Logging
Модуль 29 — Managing Cisco Devices
- Cisco IOS Integrated File System and Devices
- Stages of the Router Power-On Boot Sequence
- Loading and Managing System Images Files
- Loading Cisco IOS Configuration Files
- Validating Cisco IOS Images Using MD5
- Managing Cisco IOS Images and Device Configuration Files
- Create the Cisco IOS Image Backup
- Upgrade Cisco IOS Image
Модуль 30 — Examining the Security Threat Landscape
- Security Threat Landscape Overview
- Malware
- Hacking Tools
- Denial of Service and Distributed Denial of Service
- Spoofing
- Reflection and Amplification Attacks
- Social Engineering
- Evolution of Phishing
- Password Attacks
- Reconnaissance Attacks
- Buffer Overflow Attacks
- Man-in-the-Middle Attacks
- Vectors of Data Loss and Exfiltration
- Other Considerations
Модуль 31 — Implementing Threat Defense Technologies
- Information Security Overview
- Firewalls
- Intrusion Prevention Systems
- Protection Against Data Loss and Phishing Attacks
- Defending Against DoS and DDoS Attacks
- Introduction to Cryptographic Technologies
- IPsec Security Services
- Secure Sockets Layer and Transport Layer Security
- Wireless Security Protocols (WPA, WPA2, WPA3)
- Configure WLAN Using WPA2 PSK Using the GUI
Модуль 32 — Securing Administrative Access
- Network Device Security Overview
- Securing Access to Privileged EXEC Mode
- Securing Console Access
- Securing Remote Access
- Secure Console and Remote Access
- Configuring the Login Banner
- Limiting Remote Access with ACLs
- Enable and Limit Remote Access Connectivity
- External Authentication Options
- Secure Device Administrative Access
Модуль 33 — Implementing Device Hardening
- Securing Unused Ports
- Infrastructure ACL
- Disabling Unused Services
- Port Security
- Configure and Verify Port Security
- Mitigating VLAN Attacks
- DHCP Snooping
- Dynamic ARP Inspection
- Mitigating STP Attacks
- Implement Device Hardening
Практические работы
- Get Started with Cisco Command-Line Interface (CLI)
- Observe How a Switch Operates
- Perform Basic Switch Configuration
- Implement the Initial Switch Configuration
- Inspect TCP/IP Applications
- Configure an Interface on a Cisco Router
- Configure and Verify Layer 2 Discovery Protocols
- Implement an Initial Router Configuration
- Configure Default Gateway in Layer 2 Device and Layer 3 Device Scenarios
- Explore Packet Forwarding
- Troubleshoot Switch Media and Port Issues
- Troubleshoot Port Duplex Issues
- Configure Basic IPv6 Connectivity
- Configure and Verify IPv4 Static Routes
- Configure IPv6 Static Routes
- Implement IPv4 Static Routing
- Implement IPv6 Static Routing
- Implement Recursive and Fully Specified Static Routes
- Implement Basic Active-Standby Switching using Fully Specified Static Routes
- Configure VLAN and Trunk
- Troubleshoot VLANs and Trunk
- Configure a Router on a Stick
- Implement Multiple VLANs and Basic Routing Between the VLANs
- Configure and Verify Single-Area OSPF
- Configure and Verify Multi-Area OSPF
- Tune OSPF Metrics and Reference Bandwidth
- Configure and Verify EtherChannel
- Improve Redundant Switched Topologies with EtherChannel
- Configure and Verify IPv4 ACLs
- Implement Numbered and Named IPv4 ACLs
- Configure a Provider-Assigned IPv4 Address
- Configure Static NAT
- Configure Dynamic NAT and Port Address Translation (PAT)
- Implement PAT
- Log into the WLC
- Monitor the WLC
- Configure a Dynamic (VLAN) Interface
- Configure a DHCP Scope
- Configure a WLAN
- Define a Remote Access Dial-In User Service (RADIUS) Server
- Authentication in Cisco IOS with LDAP (Microsoft Active Directory) accounts
- Explore Management Options
- Explore the Cisco DNA™ Center
- Configure and Verify NTP
- Configure System Message Logging
- Create the Cisco IOS Image Backup
- Upgrade Cisco IOS Image
- Configure WLAN Using Wi-Fi Protected Access 2 (WPA2) Pre-Shared Key (PSK) Using the GUI
- Secure Console and Remote Access
- Enable and Limit Remote Access Connectivity
- Secure Device Administrative Access
- Configure and Verify Port Security
- Implement Dynamic ARP Inspection
- Implement Device Hardening
Стандартная продолжительность занятий
Фактическая продолжительность может быть иной — например субботние курсы обычно читаются дольше. Для уточнения информации по конкретной группе посмотрите расписание.
Что после курса?
- Подключиться к программе Knowledge Assurance и получить доступ к видеозаписям курсов и вебинаров плюс скидку на участие в онлайн-курсах.
- Зарегистрироваться в личном профиле студента учебного центра Advanced Training, чтобы получить доступ к бесплатным курсам и загрузке записей.
- Самому сделать домашнюю сетевую лабораторию для практики, бесплатно и не покупая/арендуя оборудование — про это у нас есть отдельная страница.
- Получить сертификат Advanced Training, который будет доступен по прямой ссылке и может быть распечатан в бумажном виде.
- Почитать интересные технические статьи на нашей Knowledge Base
- Посмотреть вебинары из цикла Advanced CCNA.
Личный кабинет
- 15 ноября: Обновление всей линейки образов виртуальных систем и сетевого оборудования, плюс лабораторной AT-ENSP
- 27 октября: Обновление образов, Windows Server 2022 с апдейтами на октябрь 2022, Mikrotik CHR 7.3 -> 7.6, Debian 11.4
- 19 июня: Обновление образов, Windows Server 2022 с апдейтами на июнь 2022, Mikrotik CHR 7.2 -> 7.3, обновлён Debian
- 19 июня: Новая виртуальная лаборатория — EVE-NG-AT 22.06, много изменений и улучшений.
- 20 мая: Ядро для лабы 5.17.1 -> 5.17.9, улучшение производительности и исправление ошибок запуска IOU/IOL, крайне рекомендуется к установке.
- 8 апреля: Обновление образов, Debian 11.2 -> 11.3, Mikrotik CHR 7.1 -> 7.2
- 8 апреля: Ядро для лабы 5.15.25 -> 5.17.1, улучшение производительности.
- 25 февраля: В связи со многими событиями сообщаем, что не будем менять курс доллара до 4 марта, т.е. неделю. Если планировали что-то оплатить — самое время.
- 24 февраля: Ядро для лабы 5.15.20 -> 5.15.25, опять же мелкий bugfix для повышения надёжности работы.
- 22 февраля: Скидки в честь праздника 23 февраля — в новости на сайте.
Видеозаписи
- AT-NETLAB 20.12 — Обновлённый вебинар по созданию и настройке домашней лабы
- Cisco IINS 3.0 — Шестое занятие CCNA:Security 2020
- AT-NETLAB 20.04 — Вебинар по созданию и настройке домашней лабы
- Cisco IINS 3.0 — Пятое занятие CCNA:Security 2020
- Cisco IINS 3.0 — Четвёртое занятие CCNA:Security 2020 (много RADIUS и траблшутинга, но всё закончилось хорошо)
- Cisco ICND2 3.0 — CCNA 3.0 (последнее прочтение) занятие 16
- Cisco ICND2 3.0 — CCNA 3.0 (последнее прочтение) занятие 15
- Cisco ICND2 3.0 — CCNA 3.0 (последнее прочтение) занятие 14
- Cisco ICND2 3.0 — CCNA 3.0 (последнее прочтение) занятие 13
- Cisco ICND2 3.0 — CCNA 3.0 (последнее прочтение) занятие 12