Saved searches
Use saved searches to filter your results more quickly
Cancel Create saved search
You signed in with another tab or window. Reload to refresh your session. You signed out in another tab or window. Reload to refresh your session. You switched accounts on another tab or window. Reload to refresh your session.
Have a question about this project? Sign up for a free GitHub account to open an issue and contact its maintainers and the community.
By clicking “Sign up for GitHub”, you agree to our terms of service and privacy statement. We’ll occasionally send you account related emails.
Already on GitHub? Sign in to your account
Problem bootstrapping. Stuck at 5% (conn): Connecting to a relay. (Connection timed out [WSAETIMEDOUT ]; #16
aiwwha opened this issue Jan 6, 2022 · 1 comment
Problem bootstrapping. Stuck at 5% (conn): Connecting to a relay. (Connection timed out [WSAETIMEDOUT ]; #16
aiwwha opened this issue Jan 6, 2022 · 1 comment
Comments
aiwwha commented Jan 6, 2022
I tried several times and still failed to connect successfully. Do you have a solution?
Jan 05 11:29:47.000 [notice] Bootstrapped 5% (conn): Connecting to a relay
Jan 05 11:30:54.000 [warn] Problem bootstrapping. Stuck at 5% (conn): Connecting to a relay. (Connection timed out [WSAETIMEDOUT ]; TIMEOUT; count 10; recommendation warn; host DED6892FF89DBD737BA689698A171B2392EB3E82 at 92.222.38.67:443)
Jan 05 11:30:54.000 [warn] 9 connections have failed:
Jan 05 11:30:54.000 [warn] 9 connections died in state connect()ing with SSL state (No SSL object)
Jan 05 11:31:11.000 [warn] Problem bootstrapping. Stuck at 5% (conn): Connecting to a relay. (Connection timed out [WSAETIMEDOUT ]; TIMEOUT; count 11; recommendation warn; host 7BE683E65D48141321C5ED92F075C55364AC7123 at 193.23.244.244:443)
Jan 05 11:31:11.000 [warn] 10 connections have failed:
Jan 05 11:31:11.000 [warn] 10 connections died in state connect()ing with SSL state (No SSL object)
Jan 05 11:31:11.000 [warn] Problem bootstrapping. Stuck at 5% (conn): Connecting to a relay. (Connection timed out [WSAETIMEDOUT ]; TIMEOUT; count 12; recommendation warn; host 74A910646BCEEFBCD2E874FC1DC997430F968145 at 199.58.81.140:443)
Jan 05 11:31:11.000 [warn] 11 connections have failed:
Jan 05 11:31:11.000 [warn] 11 connections died in state connect()ing with SSL state (No SSL object)
Jan 05 11:31:22.000 [warn] Problem bootstrapping. Stuck at 5% (conn): Connecting to a relay. (Connection timed out [WSAETIMEDOUT ]; TIMEOUT; count 13; recommendation warn; host B143D439B72D239A419F8DCE07B8A8EB1B486FA7 at 212.129.62.232:443)
Jan 05 11:31:22.000 [warn] 12 connections have failed:
Jan 05 11:31:22.000 [warn] 12 connections died in state connect()ing with SSL state (No SSL object)
Jan 05 11:31:41.000 [warn] Problem bootstrapping. Stuck at 5% (conn): Connecting to a relay. (Connection timed out [WSAETIMEDOUT ]; TIMEOUT; count 14; recommendation warn; host 484A10BA2B8D48A5F0216674C8DD50EF27BC32F3 at 193.70.43.76:9001)
Jan 05 11:31:41.000 [warn] 13 connections have failed:
Jan 05 11:31:41.000 [warn] 13 connections died in state connect()ing with SSL state (No SSL object)
Jan 05 11:31:48.000 [warn] Problem bootstrapping. Stuck at 5% (conn): Connecting to a relay. (Connection timed out [WSAETIMEDOUT ]; TIMEOUT; count 15; recommendation warn; host 24E2F139121D4394C54B5BCC368B3B411857C413 at 204.13.164.118:443)
Jan 05 11:31:48.000 [warn] 14 connections have failed:
Jan 05 11:31:48.000 [warn] 14 connections died in state connect()ing with SSL state (No SSL object)
The text was updated successfully, but these errors were encountered:
TROUBLESHOOTING
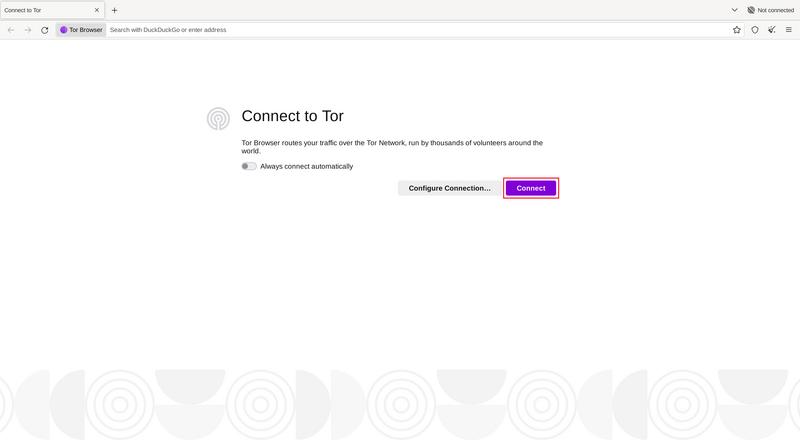
You should be able to start browsing the web using Tor Browser shortly after running the program, and clicking the «Connect» button if you are using it for the first time.
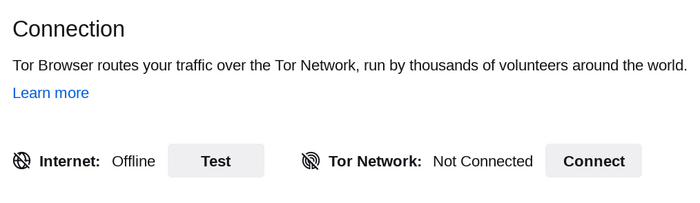
The Connection Assist informs you about the state of your Internet connection if you click on ‘Test’.
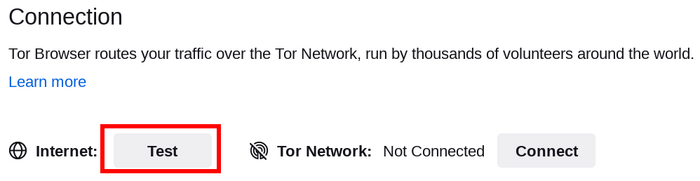
Check your Internet Connection if it says ‘Offline’. If your connection to the Tor Network is not established and it reads ‘Not Connected’ the following steps can be helpful.
QUICK FIXES
If Tor Browser doesn’t connect, there may be a simple solution. Try each of the following:
- Your computer’s system clock must be set correctly, or Tor will not be able to connect.
- Make sure another Tor Browser or instance of ‘Tor’ is not already running on your system. If you’re not sure if Tor Browser is running, restart your computer.
- Make sure that any antivirus program you have installed is not preventing Tor from running. You may need to consult the documentation for your antivirus software if you do not know how to do this.
- Temporarily disable your firewall.
- If Tor Browser was working before and is not working now your system may have been hibernating. A reboot of your system will solve the issue.
- Delete Tor Browser and install it again. If updating, do not just overwrite your previous Tor Browser files; ensure they are fully deleted beforehand.
VIEW TOR LOGS
In most cases, taking a look at the Tor logs can be helpful in diagnosing the issue. If you’re having trouble connecting, an error message may appear and you can select the option to «copy Tor log to clipboard». Then paste the Tor log into a text file or other document.
If you don’t see this option and you have Tor Browser open, you can navigate to the hamburger menu («≡»), then click on «Settings», and finally on «Connection» in the side bar. At the bottom of the page, next to the «View the Tor logs» text, click the button «View Logs. «.
Alternatively, on GNU/Linux, to view the logs right in the terminal, navigate to the Tor Browser directory and launch Tor Browser from the command line by running:
Or to save the logs to a file (default: tor-browser.log):
./start-tor-browser.desktop —log [file]
More information on this can be found on the Support Portal.
IS YOUR CONNECTION CENSORED?
If you still can’t connect, your Internet Service Provider might be censoring connections to the Tor network. Read the Circumvention section for possible solutions.
KNOWN ISSUES
Tor Browser is under constant development, and some issues are known about but not yet fixed. Please check the Known Issues page to see if the problem you are experiencing is already listed there.
-
Contributors to this page: cypherpunk
- Edit this page — Give Feedback — Permalink
Tor Relay за пять минут
Безопасность и работоспособность сети Tor напрямую зависит от количества узлов, отвечающих за пересылку трафика, — relay nodes. Организация EFF даже открыла соревнование Tor Challenge с целью простимулировать как можно большее число пользователей настроить и запустить такие узлы. Собственно говоря, именно этому нехитрому действию и посвящена статья.
Нам потребуется сервер — машина, на которой Tor Relay будет работать. Можно воспользоваться своим домашним компьютером, можно перенастроить умный роутер. Я предлагаю другой способ — использовать VPS (Virtual Private Server). Программное обеспечение Tor довольно неприхотливо и легко уживается даже на VPS с минимальной конфигурацией. Хватает 256 Mb памяти, скорее всего хватит и 128Mb. Дисковые требования также минимальны: меньше гигабайта. Стоимость такого сервера в месяц близка к стоимости чашки кофе в какой-нибудь кофейне.
Итак, регистрируем себе VPS. Для нас главное, чтобы у нее был честный внешний IP адрес. Мне нравится Yourserver, но можно использовать любой другой VPS с Linux или *BSD на борту. Как правило, после покупки вы получаете сервер, на который уже установлен один из дистрибутивов Linux. Выбирайте сами, какой вам по душе. Я буду рассказывать на примере Debian.
Сначала на VPS надо установить Tor:
# aptitude install torПо умолчанию Tor будет работать в режиме клиента сети: вы можете им воспользоваться для работы с сетью, но для для других этот экземпляр будет бесполезен. Чужой трафик через него идти не будет. Необходимо включить режим Tor Relay (пересылки пакетов). Еще мы включим Directory Service &mdsah; сервис каталогов, отвечающий за распространение информации о других tor серверах. В принципе, ничто не мешает использовать для пересылки и для каталога произвольные порты. Конфигурационный файл по умолчанию предлагает использовать порт 9001 для пересылки пакетов и 9030 для сервиса каталогов. Но, поскольку этот VPS больше ни для чего использоваться не будет, мы можем чуть схитрить и облегчить жизнь людям, сидящим за строгими межсетевыми экранами. Мы сделаем наш сервер доступным по портам 443 и 80 — по портам, которые обычно используются для www трафика.
Открываем /etc/tor/torrc и вписываем в него следующие строчки:
Nickname MyCoolNick ContactInfo Person ORPort 443 NoListen ORPort 9001 NoAdvertise DirPort 80 NoListen DirPort 9030 NoAdvertise ExitPolicy reject *:* # no exits allowed ExitPolicy reject6 *:* # no exits allowed В строчке Nickname вписываем какое-нибудь имя для этого сервера. По нему мы потом сможем контролировать работу сервера через специальные сервисы на TorProject.
В строчку ContactInfo можно вписать свои контактные данные (на случай, если кому-то захочется с вами связаться). А можно ее просто опустить, тогда наш сервер тоже никому не сможет рассказать, кто его владелец.
Последние две строчки запрещают использовать наш сервер в качестве точки выхода (Exit Node) трафика. В противном случае, Tor будет пытаться использовать наш сервер для передачи исходящего трафика сети на внешние сервера. К сожалению, не все используют Tor с благими намерениями, а если трафик покидает Tor через ваш сервер, все проблемы и последствия свалятся в том числе и на вашу голову.
Кроме того, прописанная конфигурация заставляет сервер рассказать остальным участникам сети, что сервер доступен по портам 443 для пересылки пакетов и 80 для сообщения информации о других серверах сети. При этом на самом деле сервер будет ждать сообщений на портах 9001 и 9030. В Debian Tor по умолчанию работает не из-под рута и такая конфигурация позволяет избежать проблем с подключением к портам.
С помощью iptables мы сейчас настроим необходимую связь между портами.
Если в выбранном дистрибутиве есть специальные средства настройки сетевого экрана iptables, можно воспользоваться ими. Проще и нагляднее сделать все ручками.
Создаем файл /etc/iptables.save.rules такого содержания:
# Generated by iptables-save v1.4.14 on Sat Jul 5 14:15:04 2014 *filter :INPUT ACCEPT [0:0] :FORWARD ACCEPT [0:0] :OUTPUT ACCEPT [22:1968] -A INPUT -m state --state RELATED,ESTABLISHED -j ACCEPT -A INPUT -i lo -j ACCEPT -A INPUT -d 127.0.0.0/8 ! -i lo -j REJECT --reject-with icmp-port-unreachable -A INPUT -p tcp -m tcp --dport 22 -j ACCEPT -A INPUT -p tcp -m tcp --dport 80 -j ACCEPT -A INPUT -p tcp -m tcp --dport 443 -j ACCEPT -A INPUT -p tcp -m tcp --dport 9001 -j ACCEPT -A INPUT -p tcp -m tcp --dport 9030 -j ACCEPT -A INPUT -j REJECT --reject-with icmp-port-unreachable COMMIT # Completed on Sat Jul 5 14:15:04 2014 # Generated by iptables-save v1.4.14 on Sat Jul 5 14:15:04 2014 *nat :PREROUTING ACCEPT [0:0] :INPUT ACCEPT [0:0] :OUTPUT ACCEPT [1:104] :POSTROUTING ACCEPT [1:104] -A PREROUTING -p tcp -m tcp --dport 443 -j REDIRECT --to-ports 9001 -A PREROUTING -p tcp -m tcp --dport 80 -j REDIRECT --to-ports 9030 COMMIT # Completed on Sat Jul 5 14:15:04 2014 Этим мы разрешаем работу с нашим сервером tor и доступ к ssh для удаленного администрирования.
Осталось прописать загрузку этих правил. Обычно я прописываю запуск iptables-restore в /etc/network/interfaces:
auto lo iface lo inet loopback pre-up /sbin/iptables-restore /etc/iptables.save.rules На Yourserver файл /etc/network/interfaces переписывается каждый раз при перезапуске, поэтому можно сделать чуть иначе.
Например, вставить загрузку правил iptables в /etc/rc.local. Для этого в конец файла перед exit 0 вставляем строчку
/sbin/iptables-restore /etc/iptables.save.rulesВ заключение перезапускаем сервер tor:
# service tor restartПроверяем, что мы все сделали правильно. Через некоторое время после перезапуска в файле /var/log/tor/log должна появиться строчки:
Self-testing indicates your ORPort is reachable from the outside. Excellent. Publishing server descriptor. Tor has successfully opened a circuit. Looks like client functionality is working. Self-testing indicates your DirPort is reachable from the outside. Excellent. Performing bandwidth self-test. done. Примерно через час-два, когда информация в базе данных обновится, можно зайти на globe.torproject.org и, набрав в строке поиска ник своего сервера, убедиться в том, что сеть Tor пополнилась еще одной точкой перераспределения данных.
Поначалу через новый сервер трафик идти не будет. Жизненный путь Tor Relay — это тема отдельной статьи.
UPD: Поскольку в дистрибутивах не всегда лежит последняя версия Tor, имеет смысл подключить специальные репозитории.
Так для Debian и Ubuntu можно подключить официальный репозиторий torproject.org. Для этого в /etc/apt/sources.list.d/ создаем файл torproject.list следующего содержания:
deb http://deb.torproject.org/torproject.org DISTRIBUTION mainгде вместо DISTRIBUTION вписываем версию вашего дистрибутива (например, jessie или saucy). Выполняем
# gpg --keyserver keys.gnupg.net --recv 886DDD89 # gpg --export A3C4F0F979CAA22CDBA8F512EE8CBC9E886DDD89 | apt-key add - # apt-get update # apt-get install tor Right now, Tor is protecting the privacy of millions of people like you!
This is possible because of donations from our community. If you value the privacy that Tor offers yourself and others, please make a donation today. You’ll ensure Tor continues to provide online privacy to everyone who needs it.
Connecting To Tor
Connecting To Tor
I am having trouble connecting to Tor, and I can’t figure out what’s wrong.
If you’re having trouble connecting, an error message may appear and you can select the option to «copy Tor log to clipboard». Then paste the Tor log into a text file or other document.
If you don’t see this option and you have Tor Browser open, you can navigate to the hamburger menu («≡»), then click on «Settings», and finally on «Connection» in the side bar. At the bottom of the page, next to the «View the Tor logs» text, click the button «View Logs. «.
Alternatively, on GNU/Linux, to view the logs right in the terminal, navigate to the Tor Browser directory and launch Tor Browser from the command line by running:
or to save the logs to a file (default: tor-browser.log)
./start-tor-browser.desktop —log [file]
You should see one of these common log errors (look for the following lines in your Tor log):
Common log error #1: Proxy connection failure
2017-10-29 09:23:40.800 [NOTICE] Opening Socks listener on 127.0.0.1:9150 2017-10-29 09:23:47.900 [NOTICE] Bootstrapped 5%: Connecting to directory server 2017-10-29 09:23:47.900 [NOTICE] Bootstrapped 10%: Finishing handshake with directory server 2017-10-29 09:24:08.900 [WARN] Proxy Client: unable to connect to xx..xxx..xxx.xx:xxxxx ("general SOCKS server failure") If you see lines like these in your Tor log, it means you are failing to connect to a SOCKS proxy. If a SOCKS proxy is required for your network setup, then please make sure you’ve entered your proxy details correctly. If a SOCKS proxy is not required, or you’re not sure, please try connecting to the Tor network without a SOCKS proxy.
Common log error #2: Can’t reach guard relays
11/1/2017 21:11:43 PM.500 [NOTICE] Opening Socks listener on 127.0.0.1:9150 11/1/2017 21:11:44 PM.300 [NOTICE] Bootstrapped 80%: Connecting to the Tor network 11/1/2017 21:11:44 PM.300 [WARN] Failed to find node for hop 0 of our path. Discarding this circuit. 11/1/2017 21:11:44 PM.500 [NOTICE] Bootstrapped 85%: Finishing handshake with first hop 11/1/2017 21:11:45 PM.300 [WARN] Failed to find node for hop 0 of our path. Discarding this circuit. If you see lines like these in your Tor log, it means your Tor failed to connect to the first node in the Tor circuit. This could mean that you’re on a network that’s censored.
Please try connecting with bridges, and that should fix the problem.
Common log error #3: Failed to complete TLS handshake
13-11-17 19:52:24.300 [NOTICE] Bootstrapped 10%: Finishing handshake with directory server 13-11-17 19:53:49.300 [WARN] Problem bootstrapping. Stuck at 10%: Finishing handshake with directory server. (DONE; DONE; count 10; recommendation warn; host [host] at xxx.xxx.xxx.xx:xxx) 13-11-17 19:53:49.300 [WARN] 10 connections have failed: 13-11-17 19:53:49.300 [WARN] 9 connections died in state handshaking (TLS) with SSL state SSLv2/v3 read server hello A in HANDSHAKE 13-11-17 19:53:49.300 [WARN] 1 connections died in state connect()ing with SSL state (No SSL object) If you see lines like this in your Tor log, it means that Tor failed to complete a TLS handshake with the directory authorities. Using bridges will likely fix this.
Common log error #4: Clock skew
19.11.2017 00:04:47.400 [NOTICE] Opening Socks listener on 127.0.0.1:9150 19.11.2017 00:04:48.000 [NOTICE] Bootstrapped 5%: Connecting to directory server 19.11.2017 00:04:48.200 [NOTICE] Bootstrapped 10%: Finishing handshake with directory server 19.11.2017 00:04:48.800 [WARN] Received NETINFO cell with skewed time (OR:xxx.xx.x.xx:xxxx): It seems that our clock is behind by 1 days, 0 hours, 1 minutes, or that theirs is ahead. Tor requires an accurate clock to work: please check your time, timezone, and date settings. If you see lines like this in your Tor log, it means your system clock is incorrect. Please make sure your clock is set accurately, including the correct timezone. Then restart Tor.
-
Contributors to this page: cypherpunk
- Edit this page — Suggest Feedback — Permalink
Tor Browser won’t connect, but it doesn’t seem to be an issue with censorship.
One of the most common issues that causes connection errors in Tor Browser is an incorrect system clock. Please make sure your system clock and timezone are set accurately. If this doesn’t fix the problem, see the Troubleshooting page on the Tor Browser manual.
-
Contributors to this page: cypherpunk
- Edit this page — Suggest Feedback — Permalink
«Proxy server is refusing connection» error
Proxy server errors can occur for a variety of reasons. You may try one or more of the following activities in case you encounter this error:
- If you have an antivirus, it may be interfering with the Tor service. Disable the antivirus and restart the browser.
- You should not move the Tor Browser folder from its original location to a different location. If you did this, revert the change.
- You should also check the port that you are connecting with. Try a different port from the one currently in use, such as 9050 or 9150.
- When all else fails, reinstall the browser. This time, make sure to install Tor Browser in a new directory, not over a previously installed browser.
If the error persists, please get in touch with us.
-
Contributors to this page: cypherpunk
- Edit this page — Suggest Feedback — Permalink
I cannot reach X.onion!
If you cannot reach the onion service you desire, make sure that you have entered the 56-character onion address correctly; even a small mistake will stop Tor Browser from being able to reach the site. If you are still unable to connect to the onion service, please try again later. There may be a temporary connection issue, or the site operators may have allowed it to go offline without warning.
You can also ensure that you’re able to access other onion services by connecting to DuckDuckGo’s onion service.
-
Contributors to this page: cypherpunk
- Edit this page — Suggest Feedback — Permalink